
Cybersecurity for businesses blends technical controls, clear policies, and managed expertise to safeguard data, maintain operations, and satisfy regulatory requirements for companies in Atlanta, GA. This guide walks through the services Atlanta organizations should prioritize — from endpoint protection and network defenses to backups, managed detection, compliance consulting, and incident response. Many local companies run on a mix of on‑premises, cloud, and hybrid systems; knowing how endpoint security, network controls, immutable backups, and MDR work together helps leaders make practical investments.
Throughout, you’ll find plain‑spoken definitions, useful checklists, side‑by‑side comparisons, and actionable steps geared toward small and mid‑sized businesses in the Atlanta area. Read on to learn which core services to deploy, how managed providers improve detection and response, why strong data protection matters, which compliance services help, and how incident response and disaster recovery keep your business running.
What Are the Essential Cybersecurity Services for Atlanta Businesses?
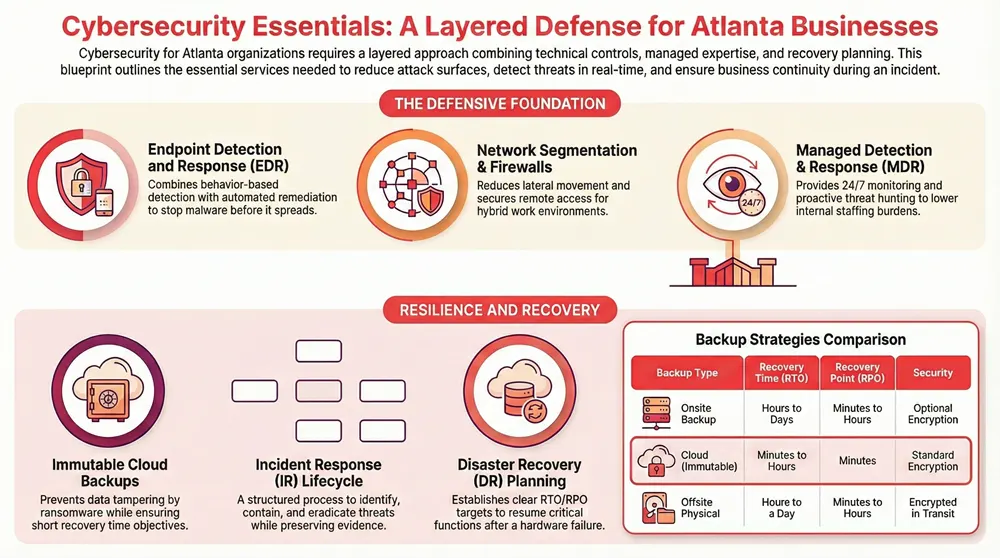
The essential services form the defensive foundation every business should consider: endpoint protection, network security, reliable backups, and managed detection & response. Together these controls reduce attack surface (endpoints and networks), surface threats early (monitoring and threat intelligence), and ensure recoverability (backups and DR), which lowers downtime and financial impact. Small and mid‑sized companies benefit from layered defenses—no single product removes all risk. Pairing behavior‑based EDR with network segmentation and immutable backups measurably improves containment and recovery. Below is a compact comparison to help decision makers evaluate coverage, monitoring, and local support needs.
This table compares common core cybersecurity services and the practical value they offer Atlanta organizations.
| Service | Typical Attributes | Business Value |
|---|---|---|
| Endpoint protection (AV/EDR) | Device malware blocking, behavior‑based detection, automated remediation | Fewer infections and faster remediation |
| Network security (firewall, VPN, segmentation) | Perimeter and internal segmentation, secure remote access, intrusion prevention | Reduces lateral movement and secures hybrid networks |
| Data backup & recovery | Scheduled/full/incremental backups, offsite or immutable storage, restore testing | Limits downtime and the cost of lost data |
| Managed detection & response (MDR) | 24/7 monitoring, threat hunting, incident containment, alert triage | Speeds detection and lowers internal staffing burden |
In practice, combining endpoint, network, backup, and MDR creates a balanced posture that reduces risk while preserving business continuity. Use these attributes to choose the right mix for your environment.
Introductory checklist for core services:
- Inventory critical assets: List devices, servers, and data so you can protect what matters most.
- Layer defenses: Use endpoint, network, and backup controls together—don’t rely on one product.
- Validate recoverability: Test backups and incident procedures regularly so restores actually work.
These steps build a solid foundation and lead naturally to selecting managed providers or internal teams for monitoring and response, which we cover next.
How Does Endpoint Protection Secure Your Business Devices?
Endpoint protection defends devices by combining traditional signature‑based antivirus with behavior‑based Endpoint Detection and Response (EDR), device controls, and patch management to stop threats before they spread. Signature AV blocks known malware, while EDR analyzes telemetry and behavior to find novel or fileless attacks—helping teams contain incidents and perform forensic analysis faster. Strong endpoint programs tie into patching and configuration management to close common exploit paths like phishing. For smaller businesses, a managed EDR service with automatic isolation and clear remediation playbooks cuts mean time to detection and containment significantly.
Below are additional insights on the role and development of Endpoint Detection and Response in modern defenses.
EDR Evolution: Modern Cybersecurity Threat Detection & Response
Endpoint Detection and Response (EDR) solutions are central to today’s cybersecurity stack, enabling organizations to detect, investigate, and respond to threats more effectively. This overview traces EDR’s evolution, explains core concepts, and highlights advances—like machine learning, behavioral analytics, and threat feeds—that strengthened EDR capabilities. It also covers practical challenges (scalability, performance, evasion techniques) and uses case studies to show how EDR integrates into broader security programs.
Evolution of endpoint detection and response (edr) in cyber security: A comprehensive review, H Kaur, 2024
Implementation checklist for endpoints:
- Deploy EDR agents across all workstations and servers and enable automated containment where appropriate.
- Enforce patching and centralized configuration management for critical software.
- Train users to spot phishing and apply device control policies consistently.
Completing this checklist hardens endpoints and prepares your team for the next defense layer: network controls and secure remote access.
What Network Security Solutions Are Available in Atlanta?
Network security protects traffic and enforces segmentation using next‑generation firewalls (NGFW), unified threat management (UTM) appliances, IDS/IPS, secure VPNs, and managed monitoring. NGFWs add application awareness, URL filtering, and threat feeds to block advanced attacks, while internal segmentation keeps attackers from reaching critical systems when an endpoint is compromised. Secure remote access—via VPNs or zero‑trust access—reduces exposure for remote workers and helps avoid cloud misconfigurations. Many Atlanta companies blend on‑site appliances with managed monitoring that correlates network anomalies with endpoint telemetry for faster detection.
Recommended architecture elements:
- NGFW at the perimeter with application‑aware rules and threat feed integration.
- Internal segmentation separating production systems and sensitive data.
- Secure remote access enforcing MFA and least‑privilege connections.
These network controls complement endpoint and backup strategies to create a layered, resilient defense.
How Can Managed Cybersecurity Services Enhance Your Atlanta Business Security?
Managed cybersecurity services—MSSP, MDR, and SOC‑as‑a‑service—deliver continuous monitoring, specialist skills, and predictable costs so Atlanta businesses detect and respond faster than they could on their own. Outsourcing 24/7 monitoring and threat hunting gives you experienced analysts, threat intelligence, and tested incident playbooks that reduce time‑to‑detection and speed containment. Managed services scale with growth, lowering the barrier for smaller organizations to use advanced defenses like proactive hunting and integrated response orchestration. Below are key benefits and a simple comparison to help you choose.
Managed services deliver clear benefits:
- 24/7 monitoring: Continuous oversight narrows the window attackers have to operate.
- Specialized expertise: Threat hunting and forensics without lengthy hiring cycles.
- Cost predictability: Fixed service models help budget for security consistently.
Summary: For many Atlanta businesses, a managed approach brings faster detection, on‑demand expertise, and better cost control versus building the same capabilities in‑house.
This table contrasts common managed security offerings available to Atlanta organizations.
| Managed Offering | Monitoring Hours | Threat Hunting | Typical Response SLA |
|---|---|---|---|
| MSSP (Managed Security Service Provider) | Business hours to 24/7 | Limited | 4–24 hours |
| MDR (Managed Detection & Response) | Typically 24/7 | Proactive hunting | 1–4 hours |
| SOC-as-a-Service | 24/7 with escalation | Advanced hunting & playbooks | <1–4 hours |
This comparison highlights that MDR and SOC‑as‑a‑service emphasize proactive hunting and faster SLAs, which usually means quicker containment and less business disruption.
Local providers add value through on‑site support and integration with office systems. Automated Business Machines (ABM), a Georgia‑based provider of office efficiency and IT solutions, bundles managed IT with IT security, secure remote access, endpoint protection, and compliance consulting for Columbus, Atlanta, Augusta, and Savannah. ABM combines managed detection and practical IT operations so containment and recovery are coordinated. If you’d like an evaluation or to request a tailored quote, consider engaging a local managed IT partner to align technical controls with daily operations.
What Are the Benefits of Managed Detection and Response Services?
MDR continuously collects endpoint and network telemetry, applies analytics and threat intelligence, and pairs automation with human threat hunting and containment to stop attackers faster. The typical MDR pipeline is: detection (ingest telemetry & analytics) → validation (human triage) → response (containment & remediation playbooks). This shortens dwell time, limits lateral movement, and yields actionable forensic reports and remediation guidance. For Atlanta businesses, MDR improves incident outcomes by blending automated detection with analyst expertise and tying into existing IT operations for fast enforcement.
MDR benefits list:
- Faster detection via continuous telemetry and analytics.
- Human validation to reduce false positives and focus fixes.
- Containment orchestration that limits impact and supports recovery.
These MDR capabilities feed directly into ransomware protection and disaster recovery planning, covered next.
How Does Ransomware Protection Safeguard Atlanta Businesses?
Ransomware protection combines prevention (patching, EDR, least‑privilege access), detection (abnormal file activity monitoring), and recovery (immutable backups and tested restores) to lower both the chance of infection and the cost to recover. Prevention closes common exploit paths through timely patching, MFA on critical systems, and user awareness training to reduce phishing success. Detection focuses on spotting unusual encryption behavior and isolating affected hosts quickly. Recovery requires immutable or offsite backups plus practiced restore procedures so you can avoid paying ransoms and minimize downtime.
Understanding ransomware’s multiple attack vectors and the strategic role of robust backups is critical when building an effective defense.
Ransomware Threats & Cybersecurity Backup Strategies
As organizations digitize more operations, keeping systems secure has become a major challenge—one that makes strong cybersecurity practices essential. Ransomware remains a leading threat: attackers encrypt data to hold organizations hostage and often combine that with data theft and extortion. Advanced groups use double‑ or triple‑extortion tactics—threatening to publish or sell stolen data or directly target customers—to increase pressure on victims.
Operational Resilience: Backup Strategies for Crisis Management in the Age of Ransomware, 2023
Ransomware prevention checklist:
- Patch and harden systems to close exploit paths.
- Deploy EDR and anomaly detection to spot behavioral indicators quickly.
- Keep immutable/offsite backups and run restore tests on a schedule.
Combining prevention, detection, and recoverability lowers operational and financial risk and supports regulatory reporting when incidents occur.
Why Is Data Protection Critical for Businesses in Atlanta, GA?
Protecting data matters because loss or exposure causes downtime, regulatory fines, reputational damage, and customer churn. Controls like encryption, strict access policies, and dependable backups reduce those risks. The basic approach is clear: control access (IAM and least privilege), encrypt data at rest and in transit, and validate recoverability with tested backups. For Atlanta businesses running hybrid cloud and local systems, misconfigurations and weak backup testing are common failure points—fixing these prevents lengthy outages and expensive recovery efforts. Below is a comparison of backup types and trade‑offs to guide planning.
| Backup Type | Recovery Time Objective (RTO) | Recovery Point Objective (RPO) | Encryption |
|---|---|---|---|
| Onsite backup | Hours to days | Minutes–hours | Optional, depends on setup |
| Offsite physical/replication | Hours to a day | Minutes–hours | Often encrypted in transit |
| Cloud backup (immutable) | Minutes–hours | Minutes | Encryption at rest and in transit standard |
This shows cloud immutable backups often provide the best mix of short RTO/RPO and built‑in encryption, which reduces incident impact and speeds restoration.
Core data protection practices include:
- Frequent backups with immutable storage to prevent tampering.
- Encryption and least‑privilege access controls to limit exposure.
- Regular restore testing to confirm recoverability and refine plans.
Once these practices are in place, integrate backup validation into your disaster recovery plan and confirm any managed provider’s policies match your recovery objectives. ABM’s managed IT and backup offerings can be part of a layered data protection strategy, delivering backup and restore services alongside ongoing managed support and compliance help when coordinated recovery is required.
How Does Secure Data Backup Prevent Business Disruption?
Secure backups prevent disruption by ensuring critical data can be restored within your RTO and RPO targets, letting operations resume after hardware failure, ransomware, or accidental deletion. The process includes choosing backup frequency (full, incremental, continuous), using immutable or offsite storage to prevent tampering, and encrypting backups so stolen copies remain unusable. Regular restore tests matter—backups that can’t be restored provide no safety. For Atlanta businesses, design backups around business‑critical systems and test restores during maintenance windows so RTO/RPO expectations stay realistic.
Backup planning checklist:
- Define RTO/RPO by system criticality and align backup schedules accordingly.
- Use immutable or offsite backups with encryption in transit and at rest.
- Perform scheduled restore tests and record results to drive improvements.
These steps feed into disaster recovery planning and let incident response move quickly from containment to restoration.
What Are Best Practices for Cloud Security in Atlanta?
Cloud security best practices include strict identity and access management (IAM), multi‑factor authentication, automated configuration checks to catch misconfigurations, and comprehensive logging and backups for cloud data. Cloud platforms follow a shared responsibility model—providers secure the infrastructure, but customers manage configuration, access, and data protection. Automated scans for misconfiguration, least‑privilege IAM roles, and continuous monitoring reduce exposure. Atlanta companies typically get stronger protection by combining cloud‑native controls with third‑party monitoring and backup services rather than relying on defaults.
Cloud security action items:
- Enable MFA and least‑privilege IAM across all cloud accounts.
- Automate configuration monitoring and remediate drift promptly.
- Ensure cloud data is backed up and logged for recovery and audits.
Putting these practices in place lowers cloud‑specific risk and supports compliance efforts outlined below.
What Compliance and Consulting Services Support Cybersecurity in Atlanta?
Compliance and consulting services help businesses identify which regulations apply, perform risk assessments, close gaps, and maintain evidence‑based controls through ongoing monitoring and audits. Consulting usually follows a clear path: assessment → gap remediation → policy and control implementation → monitoring and evidence collection. That process maps technical controls to legal obligations and cuts audit risk. Common frameworks affecting Atlanta organizations include healthcare and privacy regulations plus industry‑specific standards; consultants translate those rules into practical technical and process changes. Below are common steps organizations follow when engaging compliance consulting.
Common compliance consulting steps:
- Perform a risk and gap assessment to map current controls to requirements.
- Develop remediation and policy plans aligned with business processes.
- Implement controls and document evidence for audits and continuous monitoring.
In short: good consulting turns abstract rules into concrete policies and technical controls that align security spending with legal and customer expectations.
ABM provides IT compliance consulting alongside managed IT and security services—offering assessments, policy development, secure remote access solutions, and implementation support for Georgia businesses. Their approach focuses on fitting technical controls into daily workflows so compliance becomes part of routine operations rather than a once‑a‑year scramble. If you need a compliance assessment or help converting requirements into technical controls, consider a consultation with a local managed IT provider to map obligations to practical solutions.
How Does Cybersecurity Compliance Help Meet Atlanta’s Regulatory Requirements?
Cybersecurity compliance helps organizations meet regulations by documenting controls, standardizing processes, and collecting monitoring data that serves as audit evidence. The work begins with an assessment to identify applicable rules and control gaps, followed by prioritized remediation, policy creation, and continuous monitoring to maintain posture. Records of configurations, access logs, and test results form the evidentiary trail for due diligence during audits or incidents. For Atlanta businesses, compliance programs also shape incident notification procedures and coordinate with legal and PR teams to meet local reporting obligations.
Compliance process checklist:
- Assess and map controls to regulatory requirements.
- Remediate gaps and codify policies into operational procedures.
- Implement continuous monitoring and evidence collection for audit readiness.
Following this structure reduces compliance risk and supports faster, documented responses when incidents happen.
What Cybersecurity Consulting Services Does ABM Offer?
ABM delivers tailored IT compliance consulting, secure remote access solutions, and integrated cybersecurity strategies within its managed IT services for Georgia businesses, pairing office efficiency expertise with security‑focused IT operations. Their consulting typically starts with an assessment to find gaps, then moves to strategy, technical control implementation (endpoint protection, secure access), and ongoing monitoring to keep compliance steady. With local teams across Atlanta, Columbus, Augusta, and Savannah, ABM coordinates managed IT and security work so compliance becomes practical day‑to‑day controls. If you want a coordinated approach to IT security and compliance, ABM can assess and implement solutions that match regulatory needs.
How Can Incident Response and Disaster Recovery Protect Your Atlanta Business?
Incident response (IR) and disaster recovery (DR) protect your business by defining roles, processes, and technical controls that detect incidents, contain damage, remove threats, and restore operations to acceptable levels. IR covers the immediate lifecycle—identify, contain, eradicate, recover, and learn—while DR sets RTO and RPO targets, alternate sites, and recovery procedures to resume critical functions. Coordinated plans with legal, communications, and vendors ensure notifications and customer messages are handled correctly and on time. A tested IR/DR plan reduces downtime, limits reputational damage, and strengthens security through root‑cause fixes.
Immediate IR and DR priorities:
- Detection and triage to size up severity and scope quickly.
- Containment and eradication to stop further damage.
- Recovery and restoration aligned to RTO/RPO and verified through testing.
Below is a practitioner‑focused incident response checklist for rapid execution.
- Detect and classify the incident using telemetry and triage rules.
- Isolate affected systems to prevent lateral spread.
- Preserve forensic evidence for investigation and legal needs.
- Execute containment and remediation playbooks and restore from verified backups.
- Communicate with stakeholders including legal, PR, and regulators as required.
Completing these steps moves you from immediate stabilization to durable remediation; follow up with tabletop exercises and plan updates to close gaps.
After an incident, many organizations engage a managed provider for coordinated recovery: local firms like ABM can combine managed detection, endpoint isolation, backup restoration, and compliance reporting into a single recovery effort. If you need help designing or testing IR/DR plans, contact a managed IT provider to align capabilities with your recovery objectives.
What Are Key Steps in Incident Response Services?
Key incident response steps are detection and triage, containment, eradication, recovery, and post‑incident review—each with assigned roles, communication protocols, and measurable SLAs. Detection uses automated alerts plus analyst validation to establish scope; triage prioritizes by business impact. Containment isolates systems and applies temporary mitigations; eradication removes malware and closes exploited gaps; recovery restores from trusted backups and verifies integrity before returning to production. A formal post‑incident review captures lessons, updates playbooks, and drives preventive changes.
Incident response checklist for readiness:
- Establish detection and alerting rules tied to business priorities.
- Define containment playbooks for common incident types.
- Conduct regular tabletop exercises so teams can meet SLAs under pressure.
These steps help organizations respond in a coordinated way, minimizing downtime and preserving evidence for follow‑up.
How Does Disaster Recovery Planning Ensure Business Continuity?
Disaster recovery planning ensures continuity by identifying critical systems, setting recovery priorities, defining RTO/RPO targets, and validating restores and failover through regular testing. DR includes backups, alternate processing sites or cloud failover, documented recovery runbooks, and stakeholder communication plans. Testing—both automated restores and full failover drills—confirms targets are achievable and that staff know their roles. By aligning DR with a business impact analysis, organizations prioritize restores and set realistic expectations for leadership and customers.
Disaster recovery checklist and RTO/RPO targets example:
- Classify systems by criticality and assign RTO/RPO targets (e.g., critical systems RTO <4 hours, RPO <15 minutes).
- Document recovery procedures and keep runbooks for each critical service.
- Run scheduled failover and restore tests and revise plans based on results.
A disciplined DR program shortens time to resume operations and gives confidence that recovery will meet business needs during disruptions.
For help designing IR/DR plans that combine monitoring, backups, and compliance reporting, local managed IT providers like ABM can offer assessment, plan development, and tabletop exercises to keep plans practical and actionable.
- Request a consultation to align recovery objectives with technical capabilities.
- Prioritize critical systems and validate restore procedures with tests.
- Integrate IR/DR with compliance reporting to meet regulatory obligations after incidents.
This action‑oriented approach helps Atlanta organizations move from planning to tested readiness, reducing risk and shortening recovery timelines when incidents happen.
Frequently Asked Questions
What are the common cybersecurity threats faced by businesses in Atlanta?
Atlanta businesses commonly face phishing, ransomware, insider risks, and increasingly sophisticated persistent threats. Phishing targets employees to gain access, ransomware can lock systems and demand payment, and insider incidents happen when someone with access misuses it or makes a costly mistake. Advanced persistent threats (APTs) use stealthier techniques to stay in networks. Knowing these threats helps you prioritize defenses that reduce risk.
How can small businesses in Atlanta afford cybersecurity solutions?
Small businesses can control costs by working with managed service providers (MSPs) that offer scalable security packages. Many MSPs provide tiered pricing so you only pay for needed services. Cloud‑based security tools lower upfront hardware costs, and cyber insurance can help offset losses after an incident. Prioritize the highest‑impact measures—patching, MFA, backups, and EDR—then scale from there.
What role does employee training play in cybersecurity?
Employee training is essential. Human error is often the weakest link, so regular training on phishing recognition, password hygiene, and data handling reduces risk. Ongoing awareness programs keep staff current on new threats and reinforce security as everyone’s responsibility.
How often should businesses conduct cybersecurity assessments?
At minimum, run a full cybersecurity assessment annually. Do additional reviews after major changes—new systems, mergers, or staff shifts—and after any security incident. Regular assessments help you find vulnerabilities, stay compliant, and measure whether controls are working.
What are the key components of a disaster recovery plan?
A good disaster recovery plan defines critical systems and data, sets RTOs and RPOs, documents recovery procedures and roles, and includes a communications plan. Regular testing and updates are crucial so the plan works when you need it. Clear responsibilities and tested runbooks reduce downtime during a real event.
What is the importance of compliance in cybersecurity?
Compliance ensures you meet legal and industry obligations, protecting sensitive data and preserving customer trust. Frameworks like GDPR or HIPAA guide controls, incident reporting, and documentation. Compliance reduces regulatory risk and creates a repeatable, auditable approach to security that supports continuous improvement.



Fast indexing of website pages and backlinks on Google https://is.gd/r7kPlC
Boost your income—enroll in our affiliate program today!
Share our link, earn real money—signup for our affiliate program!
Hello https://is.gd/tvHMGJ
Monetize your audience—become an affiliate partner now!
Share your unique link and earn up to 40% commission!
Promote, refer, earn—join our affiliate program now!
Promote our brand, reap the rewards—apply to our affiliate program today!
Get started instantly—earn on every referral you make!
It’s so important to remember gaming should be fun, not a source of stress. Seeing platforms like jboss game focus on things like RTP (96-98% is great!) shows some responsibility. Balance is key, always! 😊
Earn big by sharing our offers—become an affiliate today!
Interesting read! The focus on localized payment options like GCash & PayMaya, as seen with jl1111 app casino, is smart for the Philippine market. RNG integrity is key for trust in any online gaming platform, ensuring fair play for everyone.
Promote our brand and get paid—enroll in our affiliate program!
Unlock exclusive rewards with every referral—apply to our affiliate program now!
Join our affiliate program and start earning commissions today—sign up now!
Partner with us and earn recurring commissions—join the affiliate program!
Promote our brand, reap the rewards—apply to our affiliate program today!
Be rewarded for every click—join our affiliate program today!
Excellent breakdown of Atlanta’s cybersecurity landscape. The emphasis on layered defenses—endpoint protection, network controls, and immutable backups—aligns perfectly with what enterprises need. For organizations evaluating trusted partners, verifying credentials like kkkkjl legit services ensures compliance. Proactive monitoring remains key.
Understanding variance is key to enjoying casino games long-term! Seeing platforms like jiliko app casino prioritize quick KYC (like that 2-4 hour verification!) builds trust, letting you focus on the fun. Smart move offering local payment options too. 👍
Fascinating to see how quickly online gaming evolved in the Philippines! Platforms like joinnow ph app download are really tailoring experiences for local players – mobile-first is key, it seems! A great step for accessibility.
Thefts happen. And it always feels intense. I had a client managing construction materials inventory across three cities. They lost pieces not from theft but misplacement chaos. Sounds absurd but cost them near $120k annually. While reviewing options I ended up exploring this website in a deeper way. What stood out was how asset tracking fits logistics quietly. We mapped materials movement, and within one quarter shrinkage dropped close to 27%. Staff behavior changed once visibility increased slightly. Not in a creepy way just more awareness overall. Ever thought tracking could protect collections without heavy security vibe? Can be applied to your business too.
Thefts happen. And it always feels intense. I had a client managing construction materials inventory across three cities. They lost pieces not from theft but misplacement chaos. Sounds absurd but cost them near $120k annually. While reviewing options I ended up exploring this website in a deeper way. What stood out was how asset tracking fits logistics quietly. We mapped materials movement, and within one quarter shrinkage dropped close to 27%. Staff behavior changed once visibility increased slightly. Not in a creepy way just more awareness overall. Ever thought tracking could protect collections without heavy security vibe? Can be applied to your business too.
Thefts happen. And it always feels intense. I had a client managing construction materials inventory across three cities. They lost pieces not from theft but misplacement chaos. Sounds absurd but cost them near $120k annually. While reviewing options I ended up exploring https://smartmakers.io/en/ in a deeper way. What stood out was how asset tracking fits logistics quietly. We mapped materials movement, and within one quarter shrinkage dropped close to 27%. Staff behavior changed once visibility increased slightly. Not in a creepy way just more awareness overall. Ever thought tracking could protect collections without heavy security vibe? Can be applied to your business too.